Connectivity reached new extremes, when wearable technologies enabled smart device communications to appear where analogue watches, rings, and vision-enhancing glasses used to sit. Risks of sensitive data being wrongly transmitted, as a result of malicious or non-malicious intent, grow alongside these new technologies. To ensure that this continued interconnectivity of smart devices and wearables is safe and secure, the THaW team devised, published, and patented LightTouch. This technology, conceptually compatible with existing smart bracelet and display designs, uses optical sensors on the smart device and digital radio links to create a shared secret key that enables the secure and private connection between devices.
LightTouch makes it easy for a person to securely connect their wearable device to a computerized device they encounter, for the purpose of viewing information from their device and possibly sharing that information with nearby acquaintances. To learn more, check out this recent Spotlight in IEEE Computer, or click the links below to read the journal article, the patent specifics, or the conference presentation.
Xiaohui Liang, Ronald Peterson, and David Kotz. Securely Connecting Wearables to Ambient Displays with User Intent. IEEE Transactions on Dependable and Secure Computing 17(4), pages 676–690, July 2020. IEEE. DOI: 10.1109/TDSC.2018.2840979
Xiaohui Liang, Tianlong Yun, Ron Peterson, and David Kotz. Secure System For Coupling Wearable Devices To Computerized Devices with Displays, March 2020. USPTO; U.S. Patent 10,581,606; USPTO. Download from https://patents.google.com/patent/US20170279612A1/en — Priority date 2014-08-18, Grant date 2020-03-03.
Xiaohui Liang, Tianlong Yun, Ronald Peterson, and David Kotz. LightTouch: Securely Connecting Wearables to Ambient Displays with User Intent. In IEEE International Conference on Computer Communications (INFOCOM), May 2017. IEEE. DOI: 10.1109/INFOCOM.2017.8057210
#NSFStories

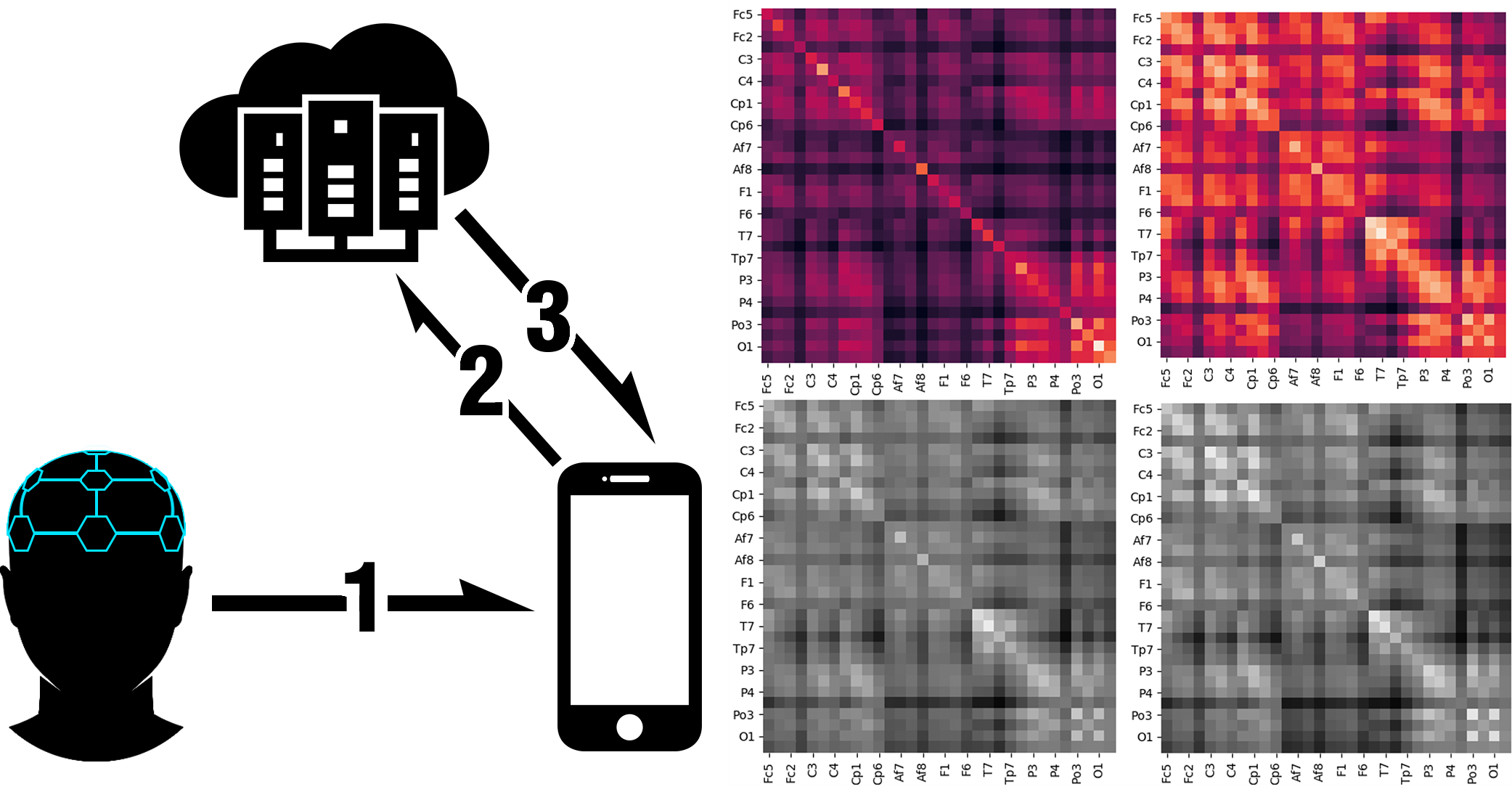 Left: IoT two factor authentication scheme – (1) After internal user-thought authentication, the device securely sends a one-time token to the IoT device. (2) The IoT device securely communicates with a server to verify the token. (3) If the token is verified, the server sends a secure confirmation reply to the IoT device, authenticating the user. Right: Proof of concept using the Psyionet BCI dataset – The top row shows the averaged covariance matrices of the extracted features of two different users thinking about the same mental task (imagining closing their fists). The bottom row shows similar features for one user thinking of two different tasks (imagine closing both fists vs both feet).
Left: IoT two factor authentication scheme – (1) After internal user-thought authentication, the device securely sends a one-time token to the IoT device. (2) The IoT device securely communicates with a server to verify the token. (3) If the token is verified, the server sends a secure confirmation reply to the IoT device, authenticating the user. Right: Proof of concept using the Psyionet BCI dataset – The top row shows the averaged covariance matrices of the extracted features of two different users thinking about the same mental task (imagining closing their fists). The bottom row shows similar features for one user thinking of two different tasks (imagine closing both fists vs both feet).