The THaW team is proud to announce the issuing of a patent for apparatuses, methods, and software for secure short-range wireless communication.
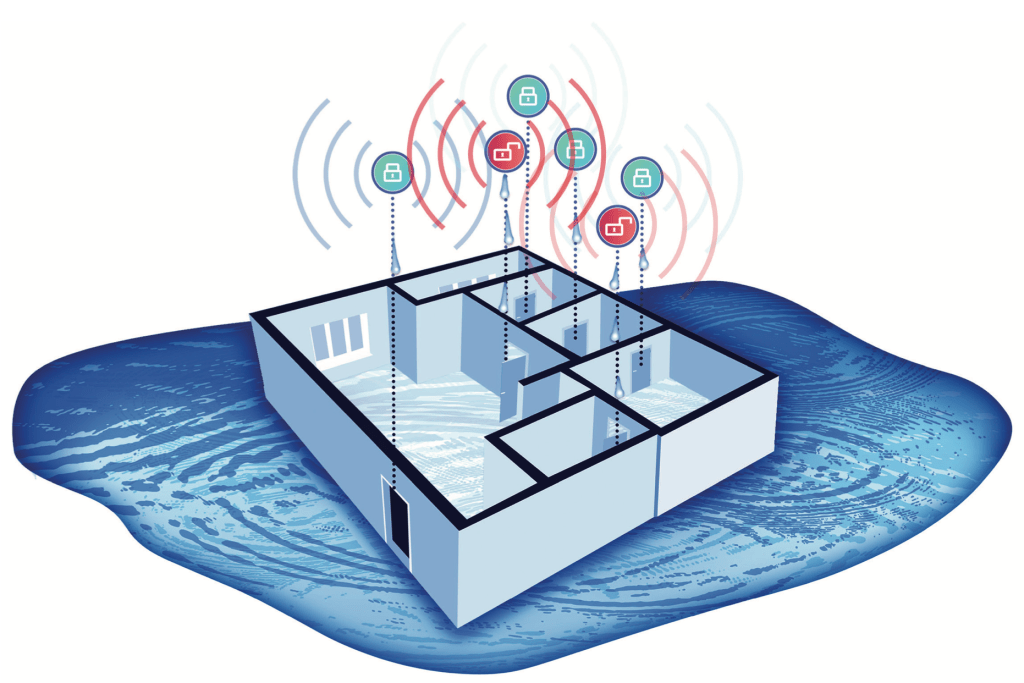
With the number and diversity of Internet of Things (IoT) devices growing, cryptography is not a blanket solution for secure message exchange. Devices may encounter dozens or hundreds of new devices each day, and many of these new IoT devices will have limited or non-existent user interfaces, making this manual secret entry even more cumbersome than configuring existing devices.
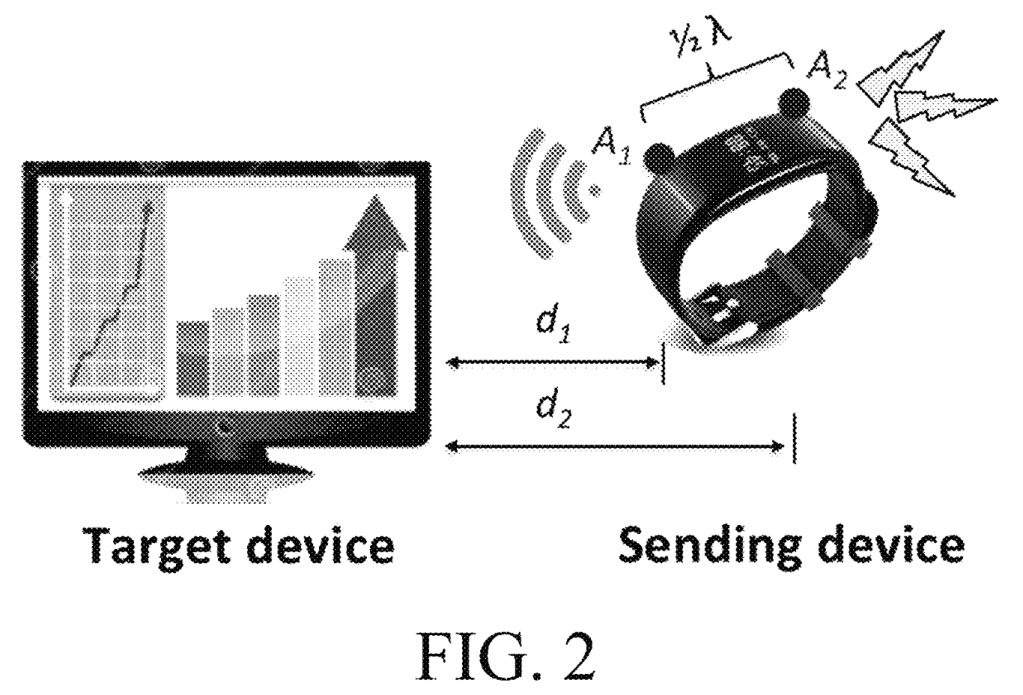
This work focuses on a secure method to wirelessly transmit data between devices that are in short-range of each other. In this setup, the sending device has two antennas and two transmitters. One transmitter sends a data signal via the first antenna, which is closer to the target device than the second antenna, and another transmits a jamming signal via the second antenna. Because of the close proximity between the target device and the first antenna, which results in a stronger signal, the receiving device can retrieve the data despite the presence of the jamming signal. This ensures a secure-communications process between the sending device and the target device.
To learn more, check out the patent. If you are interested in taking advantage of this patent, please contact us.
Timothy J. Pierson, Ronald Peterson, and David Kotz. Apparatuses, Methods, and Software for Secure Short-Range Wireless Communication. U.S. Patent 11,894,920 B2. February 06, 2024. Download from https://patents.google.com/patent/US11894920B2/en
See also: Timothy J. Pierson, Ronald Peterson, and David Kotz. Apparatuses, Methods, and Software For Secure Short-Range Wireless Communication. U.S. Patent 11,153,026, October 19, 2021. Download from https://patents.google.com/patent/US11153026B2/en
See also: Timothy J. Pierson, Travis Peters, Ronald Peterson, and David Kotz. CloseTalker: secure, short-range ad hoc wireless communication. Proceedings of the ACM International Conference on Mobile Systems, Applications, and Services (MobiSys), pages 340–352. ACM, June 2019. doi:10.1145/3307334.3326100. [Details]