A recent THaW paper was nominated for Best Paper at the IoT conference:
With the rapid growth in the number of Internet of Things (IoT) devices with wireless communication capabilities, and sensitive information collection capabilities, it is becoming increasingly necessary to ensure that these devices communicate securely with only authorized devices. A major requirement of this secure communication is to ensure that both the devices share a secret, which can be used for secure pairing and encrypted communication. Manually imparting this secret to these devices becomes an unnecessary overhead, especially when the device interaction is transient. In this work, we empirically investigate the possibility of using an out-of-band communication channel – vibration, generated by a custom smartRing – to share a secret with a compatible IoT device. Through a user study with 12 participants we show that in the best case we can exchange 85.9% messages successfully. Our technique demonstrates the possibility of sharing messages accurately, quickly, and securely as compared to several existing techniques.
To learn more, check out the video presentation here.
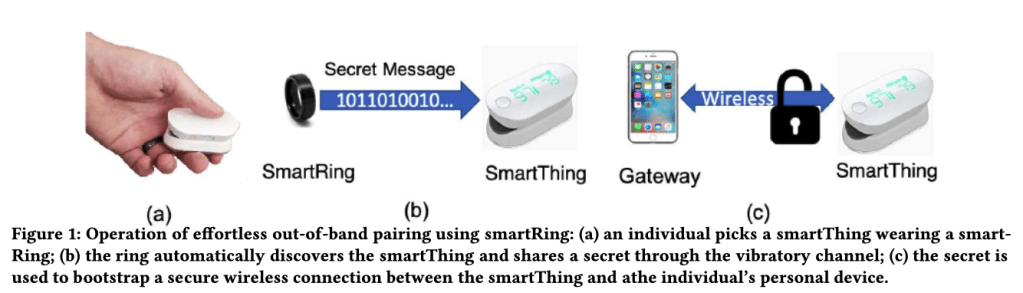
Sougata Sen and David Kotz. VibeRing: Using vibrations from a smart ring as an out-of-band channel for sharing secret keys. In Proceedings of the International Conference on the Internet of Things (IoT), page Article#13 (8 pages), October 2020. ACM. DOI: 10.1145/3341162.3343818