The THaW team is pleased to announce two new patents derived from THaW research, bringing the project total to five patents and one pending. For the complete list, visit our Tech Transfer page. The two new patents are described below.
- March 2020: Xiaohui Liang, Tianlong Yun, Ron Peterson, and David Kotz. Secure System For Coupling Wearable Devices To Computerized Devices with Displays, March 2020. USPTO; U.S. Patent 10,581,606; USPTO. Download from https://patents.google.com/patent/US20170279612A1/en — Priority date 2014-08-18, Grant date 2020-03-03. Patent describes a system enabling information from mobile health sensors (eg Fitbit) to be displayed onto nearby screens without being affected by local security threats. The scheme uses visible light sensor on the mobile device. See papers liang:lighttouch and liang:jlighttouch.
- February 2020: Timothy J. Pierson, Xiaohui Liang, Ronald Peterson, and David Kotz. Apparatus for Securely Configuring A Target Device and Associated Methods, February 2020. U.S. Patent 10,574,298; USPTO. Download from https://patents.google.com/patent/US20180191403A1/en — This is a patent. Priority date 2015-06-23, Grant date 2020-02-25. Patent based on “Wanda” device, described in other publications. Device implements a scheme for single antenna wi-fi device to determine its proximity to another wi-fi device with which it is communicating, in order to assure it is not unwittingly communicating with a distant adversary device rather than a nearby device. See paper pierson:wanda.


 The THaW team is pleased to welcome Dr. Timothy Pierson as an affiliated faculty member. Tim is no stranger to THaW – he completed his PhD within the THaW project, publishing his work about systems named
The THaW team is pleased to welcome Dr. Timothy Pierson as an affiliated faculty member. Tim is no stranger to THaW – he completed his PhD within the THaW project, publishing his work about systems named 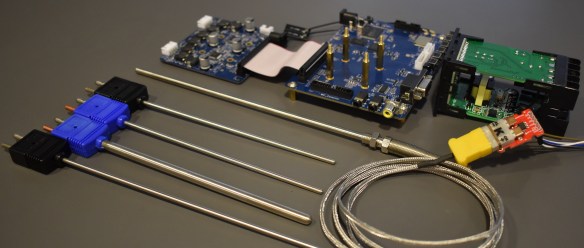
 The THaW team is pleased to welcome Prof. Michel Reece, of Morgan State University, as a new collaborator in research on security and privacy issues medical devices. Together with Tim Pierson (Dartmouth) and David Kotz (Dartmouth), Michel and her group will investigate the potential for identifying devices through features sensed at the PHY and MAC layers, and validating the authenticity of such devices.
The THaW team is pleased to welcome Prof. Michel Reece, of Morgan State University, as a new collaborator in research on security and privacy issues medical devices. Together with Tim Pierson (Dartmouth) and David Kotz (Dartmouth), Michel and her group will investigate the potential for identifying devices through features sensed at the PHY and MAC layers, and validating the authenticity of such devices.